Journal Description
Entropy
Entropy
is an international and interdisciplinary peer-reviewed open access journal of entropy and information studies, published monthly online by MDPI. The International Society for the Study of Information (IS4SI) and Spanish Society of Biomedical Engineering (SEIB) are affiliated with Entropy and their members receive a discount on the article processing charge.
- Open Access— free for readers, with article processing charges (APC) paid by authors or their institutions.
- High Visibility: indexed within Scopus, SCIE (Web of Science), MathSciNet, Inspec, PubMed, PMC, Astrophysics Data System, and other databases.
- Journal Rank: JCR - Q2 (Physics, Multidisciplinary) / CiteScore - Q1 (Mathematical Physics)
- Rapid Publication: manuscripts are peer-reviewed and a first decision is provided to authors approximately 20.8 days after submission; acceptance to publication is undertaken in 2.9 days (median values for papers published in this journal in the second half of 2023).
- Recognition of Reviewers: reviewers who provide timely, thorough peer-review reports receive vouchers entitling them to a discount on the APC of their next publication in any MDPI journal, in appreciation of the work done.
- Testimonials: See what our editors and authors say about Entropy.
- Companion journals for Entropy include: Foundations, Thermo and MAKE.
Impact Factor:
2.7 (2022);
5-Year Impact Factor:
2.6 (2022)
Latest Articles
Crude Oil Prices Forecast Based on Mixed-Frequency Deep Learning Approach and Intelligent Optimization Algorithm
Entropy 2024, 26(5), 358; https://doi.org/10.3390/e26050358 (registering DOI) - 24 Apr 2024
Abstract
Precisely forecasting the price of crude oil is challenging due to its fundamental properties of nonlinearity, volatility, and stochasticity. This paper introduces a novel hybrid model, namely, the KV-MFSCBA-G model, within the decomposition–integration paradigm. It combines the mixed-frequency convolutional neural network–bidirectional long short-term
[...] Read more.
Precisely forecasting the price of crude oil is challenging due to its fundamental properties of nonlinearity, volatility, and stochasticity. This paper introduces a novel hybrid model, namely, the KV-MFSCBA-G model, within the decomposition–integration paradigm. It combines the mixed-frequency convolutional neural network–bidirectional long short-term memory network-attention mechanism (MFCBA) and generalized autoregressive conditional heteroskedasticity (GARCH) models. The MFCBA and GARCH models are employed to respectively forecast the low-frequency and high-frequency components decomposed through variational mode decomposition optimized by Kullback–Leibler divergence (KL-VMD). The classification of these components is performed using the fuzzy entropy (FE) algorithm. Therefore, this model can fully exploit the advantages of deep learning networks in fitting nonlinearities and traditional econometric models in capturing volatilities. Furthermore, the intelligent optimization algorithm and the low-frequency economic variable are introduced to improve forecasting performance. Specifically, the sparrow search algorithm (SSA) is employed to determine the optimal parameter combination of the MFCBA model, which is incorporated with monthly global economic conditions (GECON) data. The empirical findings of West Texas Intermediate (WTI) and Brent crude oil indicate that the proposed approach outperforms other models in evaluation indicators and statistical tests and has good robustness. This model can assist investors and market regulators in making decisions.
Full article
(This article belongs to the Section Multidisciplinary Applications)
Open AccessReview
Unveiling the Future of Human and Machine Coding: A Survey of End-to-End Learned Image Compression
by
Chen-Hsiu Huang and Ja-Ling Wu
Entropy 2024, 26(5), 357; https://doi.org/10.3390/e26050357 - 24 Apr 2024
Abstract
End-to-end learned image compression codecs have notably emerged in recent years. These codecs have demonstrated superiority over conventional methods, showcasing remarkable flexibility and adaptability across diverse data domains while supporting new distortion losses. Despite challenges such as computational complexity, learned image compression methods
[...] Read more.
End-to-end learned image compression codecs have notably emerged in recent years. These codecs have demonstrated superiority over conventional methods, showcasing remarkable flexibility and adaptability across diverse data domains while supporting new distortion losses. Despite challenges such as computational complexity, learned image compression methods inherently align with learning-based data processing and analytic pipelines due to their well-suited internal representations. The concept of Video Coding for Machines has garnered significant attention from both academic researchers and industry practitioners. This concept reflects the growing need to integrate data compression with computer vision applications. In light of these developments, we present a comprehensive survey and review of lossy image compression methods. Additionally, we provide a concise overview of two prominent international standards, MPEG Video Coding for Machines and JPEG AI. These standards are designed to bridge the gap between data compression and computer vision, catering to practical industry use cases.
Full article
(This article belongs to the Special Issue Information Theory and Coding for Image/Video Processing)
Open AccessArticle
Computation of the Spatial Distribution of Charge-Carrier Density in Disordered Media
by
Alexey V. Nenashev, Florian Gebhard, Klaus Meerholz and Sergei D. Baranovskii
Entropy 2024, 26(5), 356; https://doi.org/10.3390/e26050356 - 24 Apr 2024
Abstract
The space- and temperature-dependent electron distribution
The space- and temperature-dependent electron distribution
(This article belongs to the Special Issue Recent Advances in the Theory of Disordered Systems)
►▼
Show Figures
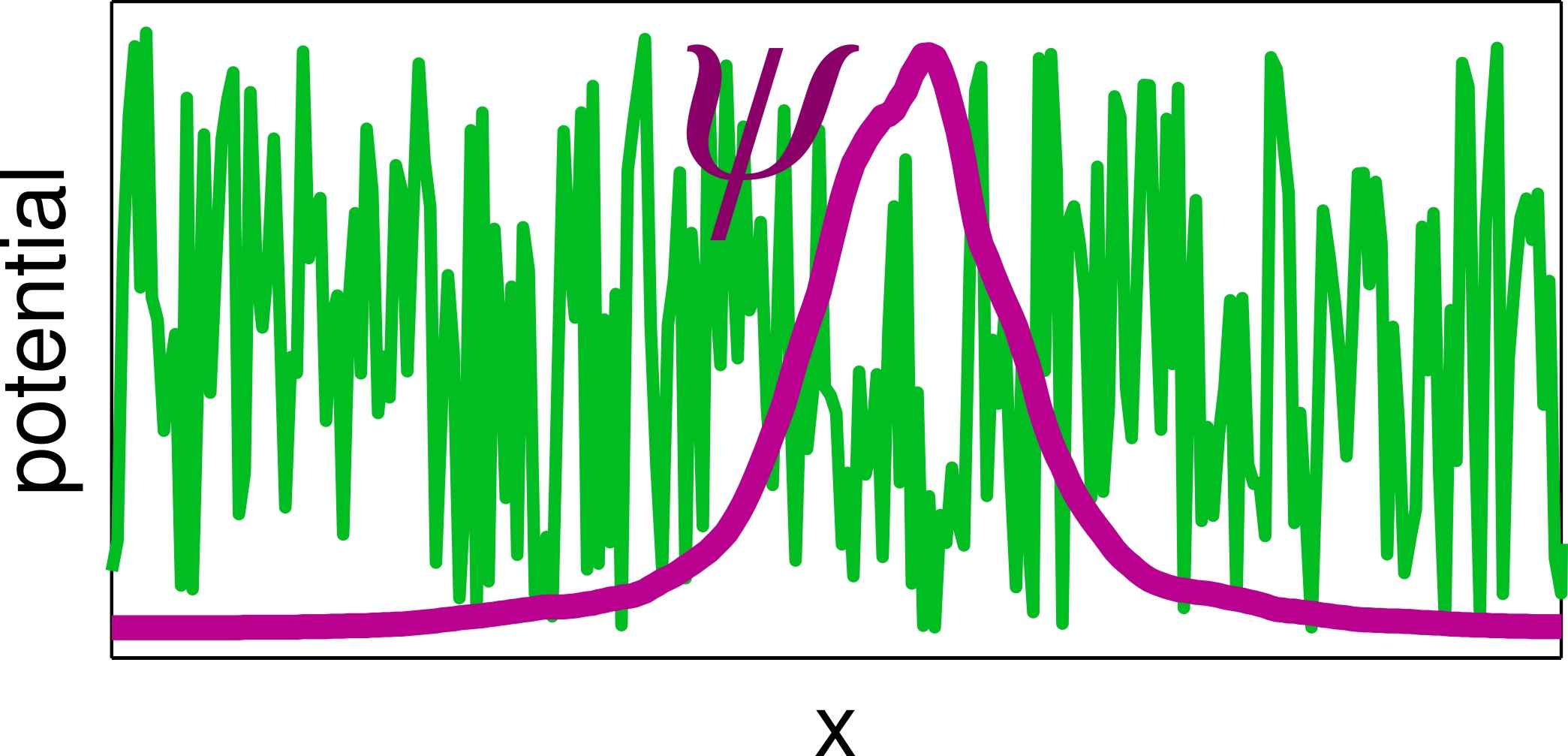
Graphical abstract
Open AccessReview
Flavor’s Delight
by
Hans Peter Nilles and Saúl Ramos-Sánchez
Entropy 2024, 26(5), 355; https://doi.org/10.3390/e26050355 - 24 Apr 2024
Abstract
Discrete flavor symmetries provide a promising approach to understand the flavor sector of the standard model of particle physics. Top-down (TD) explanations from string theory reveal two different types of such flavor symmetries: traditional and modular flavor symmetries that combine to the eclectic
[...] Read more.
Discrete flavor symmetries provide a promising approach to understand the flavor sector of the standard model of particle physics. Top-down (TD) explanations from string theory reveal two different types of such flavor symmetries: traditional and modular flavor symmetries that combine to the eclectic flavor group. There have been many bottom-up (BU) constructions to fit experimental data within this scheme. We compare TD and BU constructions to identify the most promising groups and try to give a unified description. Although there is some progress in joining BU and TD approaches, we point out some gaps that have to be closed with future model building.
Full article
(This article belongs to the Special Issue Particle Theory and Theoretical Cosmology—Dedicated to Professor Paul Howard Frampton on the Occasion of His 80th Birthday)
►▼
Show Figures
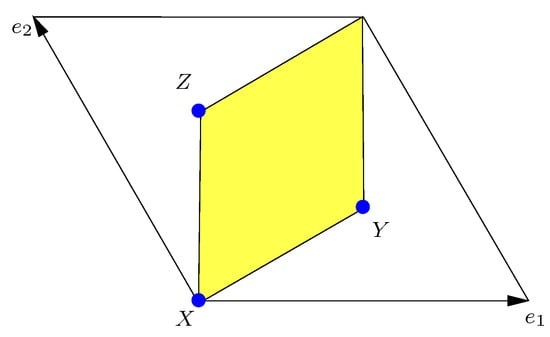
Figure 1
Open AccessArticle
Implications of Minimum Description Length for Adversarial Attack in Natural Language Processing
by
Kshitiz Tiwari and Lu Zhang
Entropy 2024, 26(5), 354; https://doi.org/10.3390/e26050354 - 24 Apr 2024
Abstract
Investigating causality to establish novel criteria for training robust natural language processing (NLP) models is an active research area. However, current methods face various challenges such as the difficulties in identifying keyword lexicons and obtaining data from multiple labeled environments. In this paper,
[...] Read more.
Investigating causality to establish novel criteria for training robust natural language processing (NLP) models is an active research area. However, current methods face various challenges such as the difficulties in identifying keyword lexicons and obtaining data from multiple labeled environments. In this paper, we study the problem of robust NLP from a complementary but different angle: we treat the behavior of an attack model as a complex causal mechanism and quantify its algorithmic information using the minimum description length (MDL) framework. Specifically, we use masked language modeling (MLM) to measure the “amount of effort” needed to transform from the original text to the altered text. Based on that, we develop techniques for judging whether a specified set of tokens has been altered by the attack, even in the absence of the original text data.
Full article
(This article belongs to the Section Information Theory, Probability and Statistics)
►▼
Show Figures
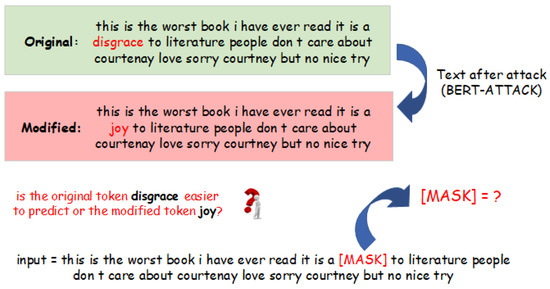
Figure 1
Open AccessArticle
LF3PFL: A Practical Privacy-Preserving Federated Learning Algorithm Based on Local Federalization Scheme
by
Yong Li, Gaochao Xu, Xutao Meng, Wei Du and Xianglin Ren
Entropy 2024, 26(5), 353; https://doi.org/10.3390/e26050353 - 23 Apr 2024
Abstract
In the realm of federated learning (FL), the exchange of model data may inadvertently expose sensitive information of participants, leading to significant privacy concerns. Existing FL privacy-preserving techniques, such as differential privacy (DP) and secure multi-party computing (SMC), though offering viable solutions, face
[...] Read more.
In the realm of federated learning (FL), the exchange of model data may inadvertently expose sensitive information of participants, leading to significant privacy concerns. Existing FL privacy-preserving techniques, such as differential privacy (DP) and secure multi-party computing (SMC), though offering viable solutions, face practical challenges including reduced performance and complex implementations. To overcome these hurdles, we propose a novel and pragmatic approach to privacy preservation in FL by employing localized federated updates (LF3PFL) aimed at enhancing the protection of participant data. Furthermore, this research refines the approach by incorporating cross-entropy optimization, carefully fine-tuning measurement, and improving information loss during the model training phase to enhance both model efficacy and data confidentiality. Our approach is theoretically supported and empirically validated through extensive simulations on three public datasets: CIFAR-10, Shakespeare, and MNIST. We evaluate its effectiveness by comparing training accuracy and privacy protection against state-of-the-art techniques. Our experiments, which involve five distinct local models (Simple-CNN, ModerateCNN, Lenet, VGG9, and Resnet18), provide a comprehensive assessment across a variety of scenarios. The results clearly demonstrate that LF3PFL not only maintains competitive training accuracies but also significantly improves privacy preservation, surpassing existing methods in practical applications. This balance between privacy and performance underscores the potential of localized federated updates as a key component in future FL privacy strategies, offering a scalable and effective solution to one of the most pressing challenges in FL.
Full article
(This article belongs to the Special Issue Information Security and Data Privacy)
►▼
Show Figures
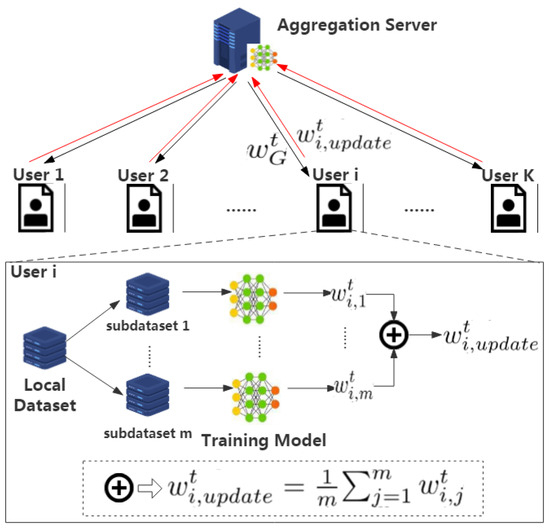
Figure 1
Open AccessArticle
DiffFSRE: Diffusion-Enhanced Prototypical Network for Few-Shot Relation Extraction
by
Yang Chen and Bowen Shi
Entropy 2024, 26(5), 352; https://doi.org/10.3390/e26050352 - 23 Apr 2024
Abstract
Supervised learning methods excel in traditional relation extraction tasks. However, the quality and scale of the training data heavily influence their performance. Few-shot relation extraction is gradually becoming a research hotspot whose objective is to learn and extract semantic relationships between entities with
[...] Read more.
Supervised learning methods excel in traditional relation extraction tasks. However, the quality and scale of the training data heavily influence their performance. Few-shot relation extraction is gradually becoming a research hotspot whose objective is to learn and extract semantic relationships between entities with only a limited number of annotated samples. In recent years, numerous studies have employed prototypical networks for few-shot relation extraction. However, these methods often suffer from overfitting of the relation classes, making it challenging to generalize effectively to new relationships. Therefore, this paper seeks to utilize a diffusion model for data augmentation to address the overfitting issue of prototypical networks. We propose a diffusion model-enhanced prototypical network framework. Specifically, we design and train a controllable conditional relation generation diffusion model on the relation extraction dataset, which can generate the corresponding instance representation according to the relation description. Building upon the trained diffusion model, we further present a pseudo-sample-enhanced prototypical network, which is able to provide more accurate representations for prototype classes, thereby alleviating overfitting and better generalizing to unseen relation classes. Additionally, we introduce a pseudo-sample-aware attention mechanism to enhance the model’s adaptability to pseudo-sample data through a cross-entropy loss, further improving the model’s performance. A series of experiments are conducted to prove our method’s effectiveness. The results indicate that our proposed approach significantly outperforms existing methods, particularly in low-resource one-shot environments. Further ablation analyses underscore the necessity of each module in the model. As far as we know, this is the first research to employ a diffusion model for enhancing the prototypical network through data augmentation in few-shot relation extraction.
Full article
(This article belongs to the Special Issue Natural Language Processing and Data Mining)
Open AccessArticle
An Efficient Image Cryptosystem Utilizing Difference Matrix and Genetic Algorithm
by
Honglian Shen and Xiuling Shan
Entropy 2024, 26(5), 351; https://doi.org/10.3390/e26050351 - 23 Apr 2024
Abstract
Aiming at addressing the security and efficiency challenges during image transmission, an efficient image cryptosystem utilizing difference matrix and genetic algorithm is proposed in this paper. A difference matrix is a typical combinatorial structure that exhibits properties of discretization and approximate uniformity. It
[...] Read more.
Aiming at addressing the security and efficiency challenges during image transmission, an efficient image cryptosystem utilizing difference matrix and genetic algorithm is proposed in this paper. A difference matrix is a typical combinatorial structure that exhibits properties of discretization and approximate uniformity. It can serve as a pseudo-random sequence, offering various scrambling techniques while occupying a small storage space. The genetic algorithm generates multiple ciphertext images with strong randomness through local crossover and mutation operations, then obtains high-quality ciphertext images through multiple iterations using the optimal preservation strategy. The whole encryption process is divided into three stages: first, the difference matrix is generated; second, it is utilized for initial encryption to ensure that the resulting ciphertext image has relatively good initial randomness; finally, multiple rounds of local genetic operations are used to optimize the output. The proposed cryptosystem is demonstrated to be effective and robust through simulation experiments and statistical analyses, highlighting its superiority over other existing algorithms.
Full article
(This article belongs to the Topic AI and Computational Methods for Modelling, Simulations and Optimizing of Advanced Systems: Innovations in Complexity)
►▼
Show Figures
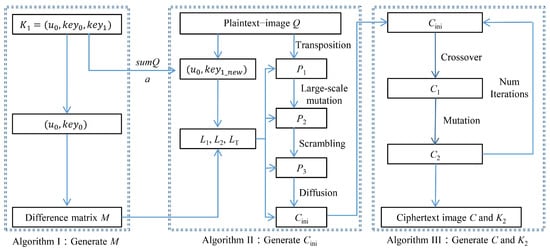
Figure 1
Open AccessArticle
Planetary Energy Flow and Entropy Production Rate by Earth from 2002 to 2023
by
Elijah Thimsen
Entropy 2024, 26(5), 350; https://doi.org/10.3390/e26050350 - 23 Apr 2024
Abstract
In this work, satellite data from the Clouds and Earth’s Radiant Energy System (CERES) and Moderate Resolution Imaging Spectroradiometer (MODIS) instruments are analyzed to determine how the global absorbed sunlight and global entropy production rates have changed from 2002 to 2023. The data
[...] Read more.
In this work, satellite data from the Clouds and Earth’s Radiant Energy System (CERES) and Moderate Resolution Imaging Spectroradiometer (MODIS) instruments are analyzed to determine how the global absorbed sunlight and global entropy production rates have changed from 2002 to 2023. The data is used to test hypotheses derived from the Maximum Power Principle (MPP) and Maximum Entropy Production Principle (MEP) about the evolution of Earth’s surface and atmosphere. The results indicate that both the rate of absorbed sunlight and global entropy production have increased over the last 20 years, which is consistent with the predictions of both hypotheses. Given the acceptance of the MPP or MEP, some peripheral extensions and nuances are discussed.
Full article
(This article belongs to the Collection Disorder and Biological Physics)
►▼
Show Figures
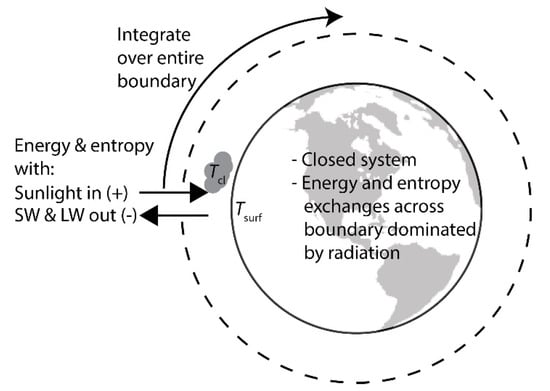
Figure 1
Open AccessArticle
Efficient Constant Envelope Precoding for Massive MU-MIMO Downlink via Majorization-Minimization Method
by
Rui Liang, Hui Li, Yingli Dong and Guodong Xue
Entropy 2024, 26(4), 349; https://doi.org/10.3390/e26040349 - 21 Apr 2024
Abstract
The practical implementation of massive multi-user multi-input–multi-output (MU-MIMO) downlink communication systems power amplifiers that are energy efficient; otherwise, the power consumption of the base station (BS) will be prohibitive. Constant envelope (CE) precoding is gaining increasing interest for its capability to utilize low-cost,
[...] Read more.
The practical implementation of massive multi-user multi-input–multi-output (MU-MIMO) downlink communication systems power amplifiers that are energy efficient; otherwise, the power consumption of the base station (BS) will be prohibitive. Constant envelope (CE) precoding is gaining increasing interest for its capability to utilize low-cost, high-efficiency nonlinear radio frequency amplifiers. Our work focuses on the topic of CE precoding in massive MU-MIMO systems and presents an efficient CE precoding algorithm. This algorithm uses an alternating minimization (AltMin) framework to optimize the CE precoded signal and precoding factor, aiming to minimize the difference between the received signal and the transmit symbol. For the optimization of the CE precoded signal, we provide a powerful approach that integrates the majorization-minimization (MM) method and the fast iterative shrinkage-thresholding (FISTA) method. This algorithm combines the characteristics of the massive MU-MIMO channel with the second-order Taylor expansion to construct the surrogate function in the MM method, in which minimizing this surrogate function is the worst-case of the system. Specifically, we expand the suggested CE precoding algorithm to involve the discrete constant envelope (DCE) precoding case. In addition, we thoroughly examine the exact property, convergence, and computational complexity of the proposed algorithm. Simulation results demonstrate that the proposed CE precoding algorithm can achievean uncoded biterror rate (BER) performance gain of roughly
(This article belongs to the Special Issue Information Theory for MIMO Systems)
►▼
Show Figures
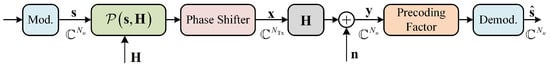
Figure 1
Open AccessArticle
Bipartite Unique Neighbour Expanders via Ramanujan Graphs
by
Ron Asherov and Irit Dinur
Entropy 2024, 26(4), 348; https://doi.org/10.3390/e26040348 - 20 Apr 2024
Abstract
We construct an infinite family of bounded-degree bipartite unique neighbour expander graphs with arbitrarily unbalanced sides. Although weaker than the lossless expanders constructed by Capalbo et al., our construction is simpler and may be closer to being implementable in practice, due to the
[...] Read more.
We construct an infinite family of bounded-degree bipartite unique neighbour expander graphs with arbitrarily unbalanced sides. Although weaker than the lossless expanders constructed by Capalbo et al., our construction is simpler and may be closer to being implementable in practice, due to the smaller constants. We construct these graphs by composing bipartite Ramanujan graphs with a fixed-size gadget in a way that generalises the construction of unique neighbour expanders by Alon and Capalbo. For the analysis of our construction, we prove a strong upper bound on average degrees in small induced subgraphs of bipartite Ramanujan graphs. Our bound generalises Kahale’s average degree bound to bipartite Ramanujan graphs, and may be of independent interest. Surprisingly, our bound strongly relies on the exact Ramanujan-ness of the graph and is not known to hold for nearly-Ramanujan graphs.
Full article
(This article belongs to the Special Issue Extremal and Additive Combinatorial Aspects in Information Theory)
►▼
Show Figures
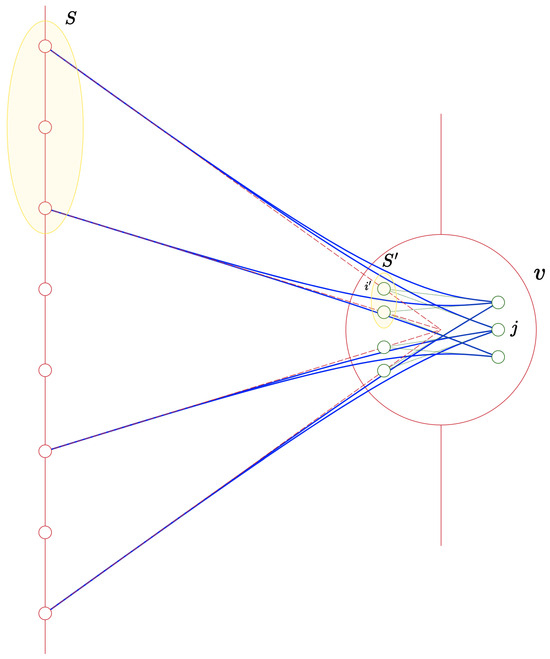
Figure 1
Open AccessArticle
Simulation of Natural Convection with Sinusoidal Temperature Distribution of Heat Source at the Bottom of an Enclosed Square Cavity
by
Min Zeng, Zhiqiang Wang, Ying Xu and Qiang Ma
Entropy 2024, 26(4), 347; https://doi.org/10.3390/e26040347 - 19 Apr 2024
Abstract
The lattice Boltzmann method is employed in the current study to simulate the heat transfer characteristics of sinusoidal-temperature-distributed heat sources at the bottom of a square cavity under various conditions, including different amplitudes, phase angles, initial positions, and angular velocities. Additionally, a machine
[...] Read more.
The lattice Boltzmann method is employed in the current study to simulate the heat transfer characteristics of sinusoidal-temperature-distributed heat sources at the bottom of a square cavity under various conditions, including different amplitudes, phase angles, initial positions, and angular velocities. Additionally, a machine learning-based model is developed to accurately predict the Nusselt number in such a sinusoidal temperature distribution of heat source at the bottom of a square cavity. The results indicate that (1) in the phase angle range from 0 to π, Nu basically shows a decreasing trend with an increase in phase angle. The decline in Nu at an accelerated rate is consistently observed when the phase angle reaches 4π/16. The corresponding Nu decreases as the amplitude increases at the same phase angle. (2) The initial position of the sinusoidal-temperature-distributed heat source Lc significantly impacts the convective heat transfer in the cavity. Moreover, the decline in Nu was further exacerbated when Lc reached 7/16. (3) The optimal overall heat transfer effect was achieved when the angular velocity of the non-uniform heat source reached π. As the angular velocity increases, the local Nu in the square cavity exhibits a gradual and oscillatory decline. Notably, it is observed that Nu at odd multiples of π surpasses that at even multiples of π. Furthermore, the current work integrates LBM with machine learning, enabling the development of a precise and efficient prediction model for simulating Nu under specific operational conditions. This research provides valuable insights into the application of machine learning in the field of heat transfer.
Full article
(This article belongs to the Special Issue Computational Thermodynamics and Its Applications)
►▼
Show Figures
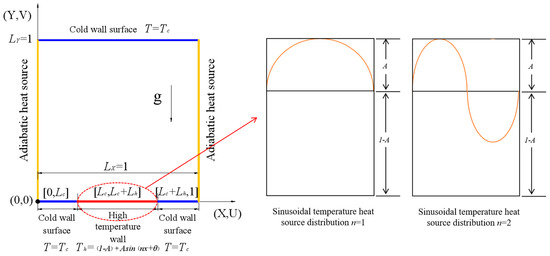
Figure 1
Open AccessArticle
Evaluating the Gilbert–Varshamov Bound for Constrained Systems
by
Keshav Goyal and Han Mao Kiah
Entropy 2024, 26(4), 346; https://doi.org/10.3390/e26040346 - 19 Apr 2024
Abstract
We revisit the well-known Gilbert–Varshamov (GV) bound for constrained systems. In 1991, Kolesnik and Krachkovsky showed that the GV bound can be determined via the solution of an optimization problem. Later, in 1992, Marcus and Roth modified the optimization problem and improved the
[...] Read more.
We revisit the well-known Gilbert–Varshamov (GV) bound for constrained systems. In 1991, Kolesnik and Krachkovsky showed that the GV bound can be determined via the solution of an optimization problem. Later, in 1992, Marcus and Roth modified the optimization problem and improved the GV bound in many instances. In this work, we provide explicit numerical procedures to solve these two optimization problems and, hence, compute the bounds. We then show that the procedures can be further simplified when we plot the respective curves. In the case where the graph presentation comprises a single state, we provide explicit formulas for both bounds.
Full article
(This article belongs to the Special Issue Discrete Math in Coding Theory)
►▼
Show Figures
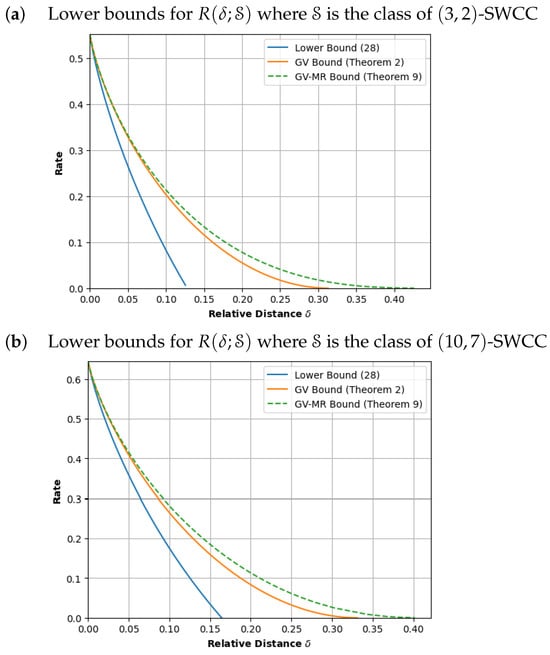
Figure 1
Open AccessArticle
Hybrid Classical–Quantum Branch-and-Bound Algorithm for Solving Integer Linear Problems
by
Claudio Sanavio, Edoardo Tignone and Elisa Ercolessi
Entropy 2024, 26(4), 345; https://doi.org/10.3390/e26040345 - 19 Apr 2024
Abstract
Quantum annealers are suited to solve several logistic optimization problems expressed in the QUBO formulation. However, the solutions proposed by the quantum annealers are generally not optimal, as thermal noise and other disturbing effects arise when the number of qubits involved in the
[...] Read more.
Quantum annealers are suited to solve several logistic optimization problems expressed in the QUBO formulation. However, the solutions proposed by the quantum annealers are generally not optimal, as thermal noise and other disturbing effects arise when the number of qubits involved in the calculation is too large. In order to deal with this issue, we propose the use of the classical branch-and-bound algorithm, that divides the problem into sub-problems which are described by a lower number of qubits. We analyze the performance of this method on two problems, the knapsack problem and the traveling salesman problem. Our results show the advantages of this method, that balances the number of steps that the algorithm has to make with the amount of error in the solution found by the quantum hardware that the user is willing to risk. The results are obtained using the commercially available quantum hardware D-Wave Advantage, and they outline the strategy for a practical application of the quantum annealers.
Full article
(This article belongs to the Special Issue Quantum Computing in the NISQ Era)
►▼
Show Figures
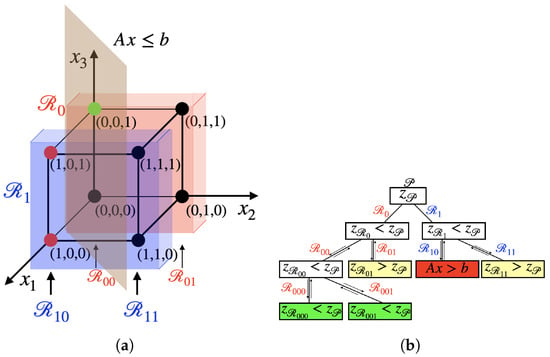
Figure 1
Open AccessArticle
Multilingual Hate Speech Detection: A Semi-Supervised Generative Adversarial Approach
by
Khouloud Mnassri, Reza Farahbakhsh and Noel Crespi
Entropy 2024, 26(4), 344; https://doi.org/10.3390/e26040344 - 18 Apr 2024
Abstract
Social media platforms have surpassed cultural and linguistic boundaries, thus enabling online communication worldwide. However, the expanded use of various languages has intensified the challenge of online detection of hate speech content. Despite the release of multiple Natural Language Processing (NLP) solutions implementing
[...] Read more.
Social media platforms have surpassed cultural and linguistic boundaries, thus enabling online communication worldwide. However, the expanded use of various languages has intensified the challenge of online detection of hate speech content. Despite the release of multiple Natural Language Processing (NLP) solutions implementing cutting-edge machine learning techniques, the scarcity of data, especially labeled data, remains a considerable obstacle, which further requires the use of semisupervised approaches along with Generative Artificial Intelligence (Generative AI) techniques. This paper introduces an innovative approach, a multilingual semisupervised model combining Generative Adversarial Networks (GANs) and Pretrained Language Models (PLMs), more precisely mBERT and XLM-RoBERTa. Our approach proves its effectiveness in the detection of hate speech and offensive language in Indo-European languages (in English, German, and Hindi) when employing only 20% annotated data from the HASOC2019 dataset, thereby presenting significantly high performances in each of multilingual, zero-shot crosslingual, and monolingual training scenarios. Our study provides a robust mBERT-based semisupervised GAN model (SS-GAN-mBERT) that outperformed the XLM-RoBERTa-based model (SS-GAN-XLM) and reached an average F1 score boost of 9.23% and an accuracy increase of 5.75% over the baseline semisupervised mBERT model.
Full article
(This article belongs to the Special Issue Advances in Complex Networks and Their Applications, from COMPLEX NETWORKS 2023)
►▼
Show Figures
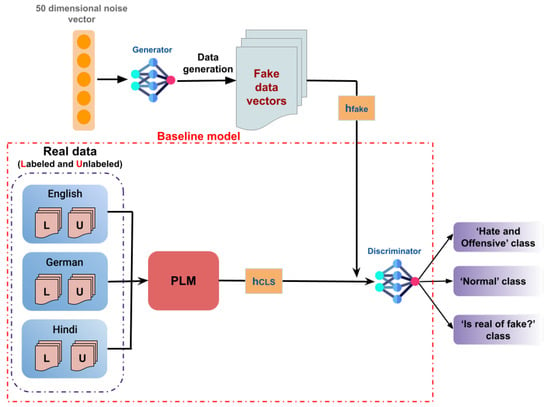
Figure 1
Open AccessOpinion
Friston, Free Energy, and Psychoanalytic Psychotherapy
by
Jeremy Holmes
Entropy 2024, 26(4), 343; https://doi.org/10.3390/e26040343 - 18 Apr 2024
Abstract
This paper outlines the ways in which Karl Friston’s work illuminates the everyday practice of psychotherapists. These include (a) how the strategic ambiguity of the therapist’s stance brings, via ‘transference’, clients’ priors to light; (b) how the unstructured and negative capability of the
[...] Read more.
This paper outlines the ways in which Karl Friston’s work illuminates the everyday practice of psychotherapists. These include (a) how the strategic ambiguity of the therapist’s stance brings, via ‘transference’, clients’ priors to light; (b) how the unstructured and negative capability of the therapy session reduces the salience of priors, enabling new top-down models to be forged; (c) how fostering self-reflection provides an additional step in the free energy minimization hierarchy; and (d) how Friston and Frith’s ‘duets for one’ can be conceptualized as a relational zone in which collaborative free energy minimization takes place without sacrificing complexity.
Full article
(This article belongs to the Special Issue From Functional Imaging to Free Energy—Dedicated to Professor Karl Friston on the Occasion of His 65th Birthday)
Open AccessArticle
Time-Varying GPS Displacement Network Modeling by Sequential Monte Carlo
by
Suchanun Piriyasatit, Ercan Engin Kuruoglu and Mehmet Sinan Ozeren
Entropy 2024, 26(4), 342; https://doi.org/10.3390/e26040342 - 18 Apr 2024
Abstract
Geodetic observations through high-rate GPS time-series data allow the precise modeling of slow ground deformation at the millimeter level. However, significant attention has been devoted to utilizing these data for various earth science applications, including to determine crustal velocity fields and to detect
[...] Read more.
Geodetic observations through high-rate GPS time-series data allow the precise modeling of slow ground deformation at the millimeter level. However, significant attention has been devoted to utilizing these data for various earth science applications, including to determine crustal velocity fields and to detect significant displacement from earthquakes. The relationships inherent in these GPS displacement observations have not been fully explored. This study employs the sequential Monte Carlo method, specifically particle filtering (PF), to develop a time-varying analysis of the relationships among GPS displacement time-series within a network, with the aim of uncovering network dynamics. Additionally, we introduce a proposed graph representation to enhance the understanding of these relationships. Using the 1-Hz GEONET GNSS network data of the Tohoku-Oki Mw9.0 2011 as a demonstration, the results demonstrate successful parameter tracking that clarifies the observations’ underlying dynamics. These findings have potential applications in detecting anomalous displacements in the future.
Full article
(This article belongs to the Special Issue Statistical Methods for Earthquake Hazard Assessment and Risk Analysis)
►▼
Show Figures
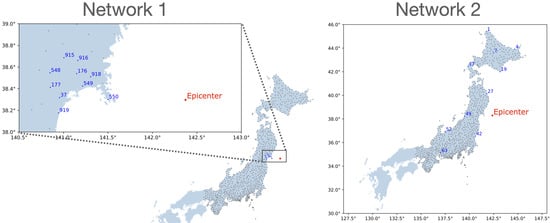
Figure 1
Open AccessArticle
Distinction of Chaos from Randomness Is Not Possible from the Degree Distribution of the Visibility and Phase Space Reconstruction Graphs
by
Alexandros K. Angelidis, Konstantinos Goulas, Charalampos Bratsas, Georgios C. Makris, Michael P. Hanias, Stavros G. Stavrinides and Ioannis E. Antoniou
Entropy 2024, 26(4), 341; https://doi.org/10.3390/e26040341 - 17 Apr 2024
Abstract
►▼
Show Figures
We investigate whether it is possible to distinguish chaotic time series from random time series using network theory. In this perspective, we selected four methods to generate graphs from time series: the natural, the horizontal, the limited penetrable horizontal visibility graph, and the
[...] Read more.
We investigate whether it is possible to distinguish chaotic time series from random time series using network theory. In this perspective, we selected four methods to generate graphs from time series: the natural, the horizontal, the limited penetrable horizontal visibility graph, and the phase space reconstruction method. These methods claim that the distinction of chaos from randomness is possible by studying the degree distribution of the generated graphs. We evaluated these methods by computing the results for chaotic time series from the 2D Torus Automorphisms, the chaotic Lorenz system, and a random sequence derived from the normal distribution. Although the results confirm previous studies, we found that the distinction of chaos from randomness is not generally possible in the context of the above methodologies.
Full article
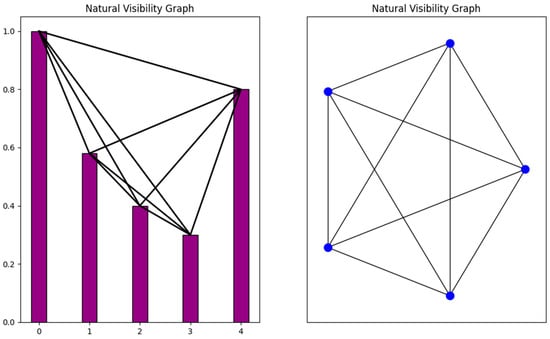
Figure 1
Open AccessArticle
Irradiation-Hardening Model of TiZrHfNbMo0.1 Refractory High-Entropy Alloys
by
Yujun Fan, Xuejiao Wang, Yangyang Li, Aidong Lan and Junwei Qiao
Entropy 2024, 26(4), 340; https://doi.org/10.3390/e26040340 - 17 Apr 2024
Abstract
In order to find more excellent structural materials resistant to radiation damage, high-entropy alloys (HEAs) have been developed due to their characteristics of limited point defect diffusion such as lattice distortion and slow diffusion. Specially, refractory high-entropy alloys (RHEAs) that can adapt to
[...] Read more.
In order to find more excellent structural materials resistant to radiation damage, high-entropy alloys (HEAs) have been developed due to their characteristics of limited point defect diffusion such as lattice distortion and slow diffusion. Specially, refractory high-entropy alloys (RHEAs) that can adapt to a high-temperature environment are badly needed. In this study,
(This article belongs to the Special Issue Recent Advances in Refractory High Entropy Alloys)
►▼
Show Figures
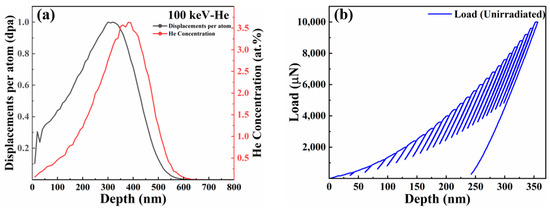
Figure 1
Open AccessReview
Advances in Adjoint Functions of Connection Number in Water Resources Complex Systems: A Systematic Review
by
Liangguang Zhou, Juliang Jin, Rongxing Zhou, Yi Cui, Chengguo Wu, Yuliang Zhou, Shibao Dai and Yuliang Zhang
Entropy 2024, 26(4), 339; https://doi.org/10.3390/e26040339 - 16 Apr 2024
Abstract
The adjoint function of connection number has unique advantages in solving uncertainty problems of water resource complex systems, and has become an important frontier and research hotspot in the uncertainty research of water resource complex problems. However, in the rapid evolution of the
[...] Read more.
The adjoint function of connection number has unique advantages in solving uncertainty problems of water resource complex systems, and has become an important frontier and research hotspot in the uncertainty research of water resource complex problems. However, in the rapid evolution of the adjoint function, some problems greatly limit the application of the adjoint function in the research of water resources. Therefore, based on bibliometric analysis, development, practical application issues, and prospects of the hot directions are analyzed. It is found that the development of the connection number of water resource set pair analysis can be divided into three stages: (1) relatively sluggish development before 2005, (2) a period of rapid advancement in adjoint function research spanning from 2005 to 2017, and (3) a subsequent surge post-2018. The introduction of the adjoint function of connection number promotes the continuous development of set pair analysis of water resources. Set pair potential and partial connection number are the crucial research directions of the adjoint function. Subtractive set pair potential has rapidly developed into a relatively independent and important trajectory. The research on connection entropy is comparatively less, which needs to be further strengthened, while that on adjacent connection number is even less. The adjoint function of set pair potential can be divided into three major categories: division set pair potential, exponential set pair potential, and subtraction set pair potential. The subtraction set pair potential, which retains the original dimension and quantity variation range of the connection number, is widely used in water resources and other fields. Coupled with the partial connection number, a series of new connection number adjoint functions have been developed. The partial connection number can be mainly divided into two categories: total partial connection number, and semi-partial connection number. Among these, the calculation expression and connotation of total partial connection numbers have not yet reached a consensus, accompanied by the slow development of high-order partial connection numbers. Semi-partial connection number can describe the mutual migration movement between different components of the connection number, which develops rapidly. With the limitations and current situation described above, promoting the exploration and application of the adjoint function of connection number in the field of water resources and other fields of complex systems has become the focus of future research.
Full article
(This article belongs to the Topic Complex Systems and Artificial Intelligence)
►▼
Show Figures
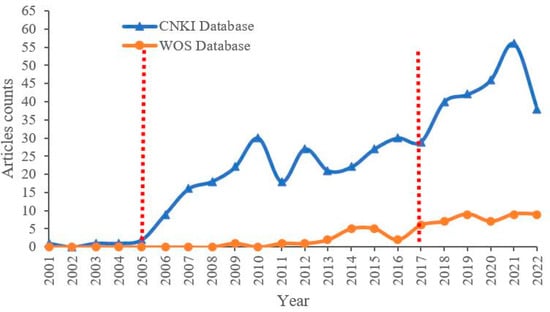
Figure 1

Journal Menu
► ▼ Journal Menu-
- Entropy Home
- Aims & Scope
- Editorial Board
- Reviewer Board
- Topical Advisory Panel
- Video Exhibition
- Instructions for Authors
- Special Issues
- Topics
- Sections & Collections
- Article Processing Charge
- Indexing & Archiving
- Editor’s Choice Articles
- Most Cited & Viewed
- Journal Statistics
- Journal History
- Journal Awards
- Society Collaborations
- Conferences
- Editorial Office
Journal Browser
► ▼ Journal Browser-
arrow_forward_ios
Forthcoming issue
arrow_forward_ios Current issue - Vol. 26 (2024)
- Vol. 25 (2023)
- Vol. 24 (2022)
- Vol. 23 (2021)
- Vol. 22 (2020)
- Vol. 21 (2019)
- Vol. 20 (2018)
- Vol. 19 (2017)
- Vol. 18 (2016)
- Vol. 17 (2015)
- Vol. 16 (2014)
- Vol. 15 (2013)
- Vol. 14 (2012)
- Vol. 13 (2011)
- Vol. 12 (2010)
- Vol. 11 (2009)
- Vol. 10 (2008)
- Vol. 9 (2007)
- Vol. 8 (2006)
- Vol. 7 (2005)
- Vol. 6 (2004)
- Vol. 5 (2003)
- Vol. 4 (2002)
- Vol. 3 (2001)
- Vol. 2 (2000)
- Vol. 1 (1999)
Highly Accessed Articles
Latest Books
E-Mail Alert
News
Topics
Topic in
Algorithms, Computation, Entropy, Fractal Fract, MCA
Analytical and Numerical Methods for Stochastic Biological Systems
Topic Editors: Mehmet Yavuz, Necati Ozdemir, Mouhcine Tilioua, Yassine SabbarDeadline: 10 May 2024
Topic in
Algorithms, Diagnostics, Entropy, Information, J. Imaging
Application of Machine Learning in Molecular Imaging
Topic Editors: Allegra Conti, Nicola Toschi, Marianna Inglese, Andrea Duggento, Matthew Grech-Sollars, Serena Monti, Giancarlo Sportelli, Pietro CarraDeadline: 31 May 2024
Topic in
Education Sciences, Entropy, JAL, Societies, Sustainability
Sustainability in Aging and Depopulation Societies
Topic Editors: Shiro Horiuchi, Gregor Wolbring, Takeshi MatsudaDeadline: 15 June 2024
Topic in
Buildings, Energies, Entropy, Resources, Sustainability
Advances in Solar Heating and Cooling
Topic Editors: Salvatore Vasta, Sotirios Karellas, Marina Bonomolo, Alessio Sapienza, Uli JakobDeadline: 30 June 2024

Conferences
22–26 November 2024
2024 International Conference on Science and Engineering of Electronics (ICSEE'2024) Wuhan, China

28–31 May 2024
XXII Conference on Non-equilibrium Statistical Mechanics and Nonlinear Physics—MEDYFINOL 2024

Special Issues
Special Issue in
Entropy
The Landauer Principle and Its Implementations in Physics, Chemistry and Biology: Current Status, Critics and Controversies
Guest Editor: Edward BormashenkoDeadline: 30 April 2024
Special Issue in
Entropy
Information Theory for Interpretable Machine Learning
Guest Editors: Marco Piangerelli, Sotiris KotsiantisDeadline: 15 May 2024
Special Issue in
Entropy
Entropy, Statistical Evidence, and Scientific Inference: Evidence Functions in Theory and Applications
Guest Editors: Brian Dennis, Mark L. Taper, Jose Miguel PoncianoDeadline: 31 May 2024
Special Issue in
Entropy
Nonlinear Dynamics in Cardiovascular Signals
Guest Editor: Claudia LermaDeadline: 15 June 2024
Topical Collections
Topical Collection in
Entropy
Algorithmic Information Dynamics: A Computational Approach to Causality from Cells to Networks
Collection Editors: Hector Zenil, Felipe Abrahão
Topical Collection in
Entropy
Wavelets, Fractals and Information Theory
Collection Editor: Carlo Cattani
Topical Collection in
Entropy
Entropy in Image Analysis
Collection Editor: Amelia Carolina Sparavigna